WordPress sites get hacked all the time. WordPress is the most popular CMS worldwide powering roughly 35% of all the sites online so, as expected, there’s a lot of attention around it. Of course, the more popular a software is, the more attention it gets. Now you may ask yourself, why do WordPress sites get hacked?
Why do WordPress sites get hacked? What is the benefit for the hackers?
There’s actually several reasons for this. Usually, hackers infect sites with backdoors which eventually use as botnets for DDoS (distributed denial of service) attacks. If you are unfamiliar with the term DDoS attack - it’s basically several infected sites (even thousands) being used to send packets of information to a single site at the same time, causing the server to overload and crash, and making the site inaccessible (hence the term denial of service).
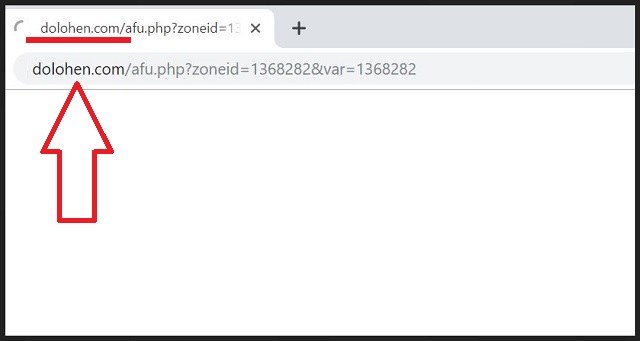
One other popular reason why your site would get hacked is to redirect it to a spam/advert site. This is also the result of the Dolohen hack. By doing that, hackers redirect all your traffic to advert sites generating revenue through 3rd party networks. Other reasons for site hacks include: data stealing, google ad swapping to steal revenue, simply stop it from working from competitors and more.
Why is it so easy for WordPress sites to get hacked?
Simply put, 2 main reasons: Popularity and open source. What do we mean by that? Let’s analyse:
Popularity: As we mentioned before, the more people involved in a project, the more it gets exploited. Since WordPress powers more than 80 million sites worldwide, it’s absolutely normal for hackers to target it.
Open Source: WordPress is open source. What does that mean? The actual code is available to everyone. Why is this a problem? Anyone can read the code, mess with it and of course, find vulnerabilities.
Also, anyone can code a plugin or a theme and submit it to the WordPress repository making it available to download and install. Unfortunately, the approval process for this does not involve backdoor checking, therefore, there's always a chance a 'not very popular' plugin to contain malicious code.
The (in)famous Dolohen hack. What is it and what does it do to your site?
Now let’s talk about the main reason you are here. The infamous dolohen hack. This type of hack is basically a classic SQL injection, injecting malicious javascript to your site. Hackers use a backdoor on your site to make a MySQL connection to the site’s database and inject the malicious code on every single page and post of your site. So every time a page or post is accessed, the malicious javascript code gets triggered causing your site to redirect.
How do I identify the Dolohen hack?
Identifying the Dolohen hack on your site is very easy. All you need to do is access your site’s database using a database management tool (phpMyAdmin), then select the site’s database, go to Search and search for ‘dolohen’. Before searching, make sure you are searching through all the tables of the database. If your site is infected, you should see several results, usually in the tables wp_post and wp_postmeta.
How do I prevent my site from being infected with the Dolohen hack?
There are no exact steps to guarantee a dolohen-free site. Measures can be taken both on the site and on the server side. Let’s talk about the top priority and easiest things you must do:
- Update your WordPress site and make sure you are using the latest version at all times.
- Always update your Plugins to the latest versions. Use plugins that are constantly maintained by their authors. Do not acquire plugins from non-legit sources.
- Same thing goes for the theme you are using.
- Delete any unused themes or plugins.
- Use a security plugin like Wordfence or Cerber
More advanced security measures can be taken on the server side like: lockdown directories using .htaccess, stop PHP code from being executed from places where it’s not supposed to, make sure files have the right permissions, block SQL injection with mod_security and more.
Here at fixed, we’ve cleaned and secured more than 2000s sites so far. We can help you clean the dolohen hack or any type of infection and secure your web hosting. Talk to us to get your site cleaned now. ETA for hack cleanups is just a few hours.