Similar to any software out there, WordPress plugins can have vulnerabilities from time to time. They can be flaws, glitches or weak coding of software. This enables hackers to break into your site and take control. And fixing a hacked website can be a nightmare.
When choosing your plugins, pick wisely. Make sure to check last update date and how many active installations it has.
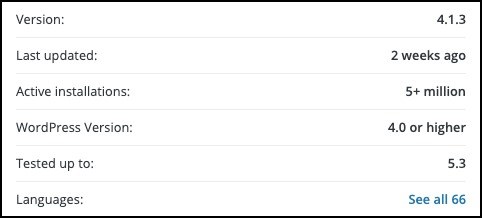
A plugins’ popularity does not mean it’s not vulnerable to attacks. Millions of users don’t bother updating to newer versions, skipping the new security patches and making the plugin easy to hack.
Let’s discuss first the most common vulnerabilities you may encounter with plugins.
1. Arbitrary file viewing What is a source file? This is a file, containing the list of program instructions as well as other essential coding data. Usually most plugins have security checks in place which allows you to view only certain source files. 3rd party viewers cannot see any sensitive data.
Wp-config.php file, for example, contains details about your database and the needed credentials for access. If hackers manage to get this information, they could easily break into the database and add malicious scripts.
2. Arbitrary file upload In some cases, users are allowed to upload their own file, such as pdf or profile picture. A lot of plugins lack security which helps identify the uploaded files and their content.
This means that a hacker could easily upload a .php file containing executable code, instead of a simple pdf. A new admin account can be created in this case or any type of other backdoor which then grants them access to your site.
3. SQL injections One of the most common vulnerabilities is a SQL injection. It exploits areas which send important information to the database. This happens when the plugin can’t validate the information being send to the database.
A hacker can simply insert their own scripts in these inputs, which will not be validated before being send to the database. Once there, the malicious malware will run. This will give the hacker full access, like creating a new admin account, injecting spam links or changing your password.
4. Privilege escalation Once getting access to any type of user on your website, hackers can escalate privileges to an admin. This will give them full control of your website.
5. Remote execution evaluation With the help of cross-site scripting vulnerabilities, hackers can make changes to any elements and injections any type of malicious software.
6. Cross-site scripting (XSS) Most commonly known as XSS, this is a certain type of injections which hackers use to add malicious scripts to sites. It most often happens using vulnerabilities in comments. Is targets the users and not the website.
Which are the most vulnerable WordPress plugins?
We’ve gathered the most popular plugins on the market, which had a number of vulnerabilities in them. Please note, that they were patched almost straight away. If any of these plugins are present on your site, make sure to update them immediately, or delete them if you are not using them.
1. WooCommerce

With over 5 millions active installations, WooCommerce is one of the most popular plugins out there.
It helps WordPress sites become e-commerce stores. Websites such as those, usually store sensitive data – payment and personal details, making the need for good security essential. Although the plugin is very well maintained, it does have its vulnerabilities. A total of 19 vulnerabilities were found since 2014. They included XSS, privilege escalation flaws and SQL injections.
In November 2018 it was discovered that anyone with the role of Shop manager can control the entire site when it’s powered by WooCommerce. With version 3.4.6 the problem was fixed.
Security issues with WooCommerce as dealt with quickly as the team receives regular updates.
2. Ultimate member

This plugin enables site owners to integrate a sign-up option for memberships and user-profiles. It has over 100,000 active installations.
13 vulnerabilities were found since 2017, which include XSS flaws and Arbitrary file read. If an admin account created a file or image upload option for one of the forms on their site, it gave all users access to any file on the server.
Developers, however, are constantly on the lookout for any issues and releasing new version.
3. Yoast SEO
Anyone using Yoast SEO know it’s super easy and straight-forward to use. It helps with improving site SEO for pages and posts from your WP Dashboard.
The plugin has immense popularity with over 5 million active installs. However, a total of 10 vulnerabilities were discovered since 2010. Some of them include XSS and remote code execution.
The most recent one was discovered in version 9.1. It affected all users with the SEO Manager role. It included the not so common issue Race condition, where the plugin expects a certain process to happen in a special sequence, but when that sequence changes, this vulnerability appears.
The problem was fixed with version 9.2, but currently only around 20% of its users are using the new version.
4. Ninja Forms
With its over 1 million subscribers, Ninja Form is mostly known as the ultimate free contact form plugin.
Some of its 10 known vulnerabilities so far include remote code execution, XSS and SQL injections.
5. Wordfence

Wordfence provides malware and firewall scanning services and currently has over 2 million active installations. Although it’s a security plugin, often such apps are the main targets of hackers.
The number of patched vulnerabilities in the past is 10, until 2018, when multiple new flaws were discovered which include XSS. With the release of version 5.2.3 the issue was solved.
6. NextGen Gallery

NextGEN enables site owners to create slideshows or display an image gallery. It’s very popular among bloggers and photographers, reaching over 1.5 million downloads.
A couple of security issues were found over the years. 7 vulnerabilities were found which include SQL injection, XSS and remote code execution.
The most recent one occurred in 2019, where hackers could execute commands remotely on sites which had the plugin installed. The issue was solved later that year with version 3.2.11.
7. JetPack

An all-in-one general WP management tool with over 5 million installs. It provides users with a range of utilities and functionalities. As it manages the coding, any issues with security could lead to a compromised site.
So far, the plugin has seen 5 vulnerabilities, with the most severe one found in 2018. An XSS vulnerability allowed hackers to inject code to the site’s server.
In November 2019, JetPack released the 7.9.1 version with the patch.
8. All-in-One SEO Pack
With over 50 million downloads since it’s release in 2007 and 2 million active installations, this plugin is one of the most popular on the market.
So far 2 vulnerabilities were discovered, which include privilege escalation flaws and XSS. In 2018 with version 3.2.6 an XSS flaw was found. It was used to help hackers get access to an admin account, they had the option to execute their own codes and even compromise the server.
Since then, the problem was solved, but make sure to use only the latest version.
9. Elementor
Elementor is widely popular plugin as it’s one of the most used drag-and-drop page builders. With its over 3 million active installations, it brings ease to a lot of users looking to build their own site.
In 2017 two vulnerabilities related to privilege escalation were discovered. They were found in the template library, history and page settings. They were fixed with version 1.8.8 and 1.8.9, and no other issues were found since then.
10. Contact Form 7

With the help of this plugin, users can design their own contact forms. It doesn’t store any personal data, but site owners can make certain changes to the settings and still track at least some amount of data.
So far, two known vulnerabilities were discovered. In 2018, a flaw with privilege escalation was located, which allowed hackers to upload malicious flaws into the website’s directory. This opens the possibilities for more severe attacks in the future.
What security measures can you take to protect your site?
To avoid any problems with your plugins, it’s best to use only trusted ones. Check the active installations and last update date. This shows whether the plugin has been regularly maintained.
- Install a Security Plugin
Make sure to always have a trusted security plugin on your website. It will make regular scanning for malicious malware and if any are found, it will notify you immediately.
- Regularly update your site
Developers announce regular updates for the WP core, plugins and themes. Those updates assist with functionality, remove bugs and glitches, as well as add new features. They also carry important security patches, fixing any security issues.
Implement Site Hardening WP recommends that you take certain security measures which will help significantly reduce the risk of attacks. This may include using stronger credentials, disabling the file editor in plugins and themes, resetting passwords, and even changing security keys and salts.
Avoid Pirate Plugins
Never use cracked version of plugins or pirated ones. Although it will provide you with premium features for free, it will also compromise your security as they often come will malicious malware embedded in them.
- Delete themes and plugins you are not using
Remove all unused plugins and themes. The more plugins you have on your site, the higher the chances of getting hacked.
Conclusion
You can often see security issues even with the most secure software. If you find one in your plugins, update it immediately to the latest version.
You can always contact Fixed.Net if you have any suspicions your plugins are compromised and we will do a full security audit on your site!